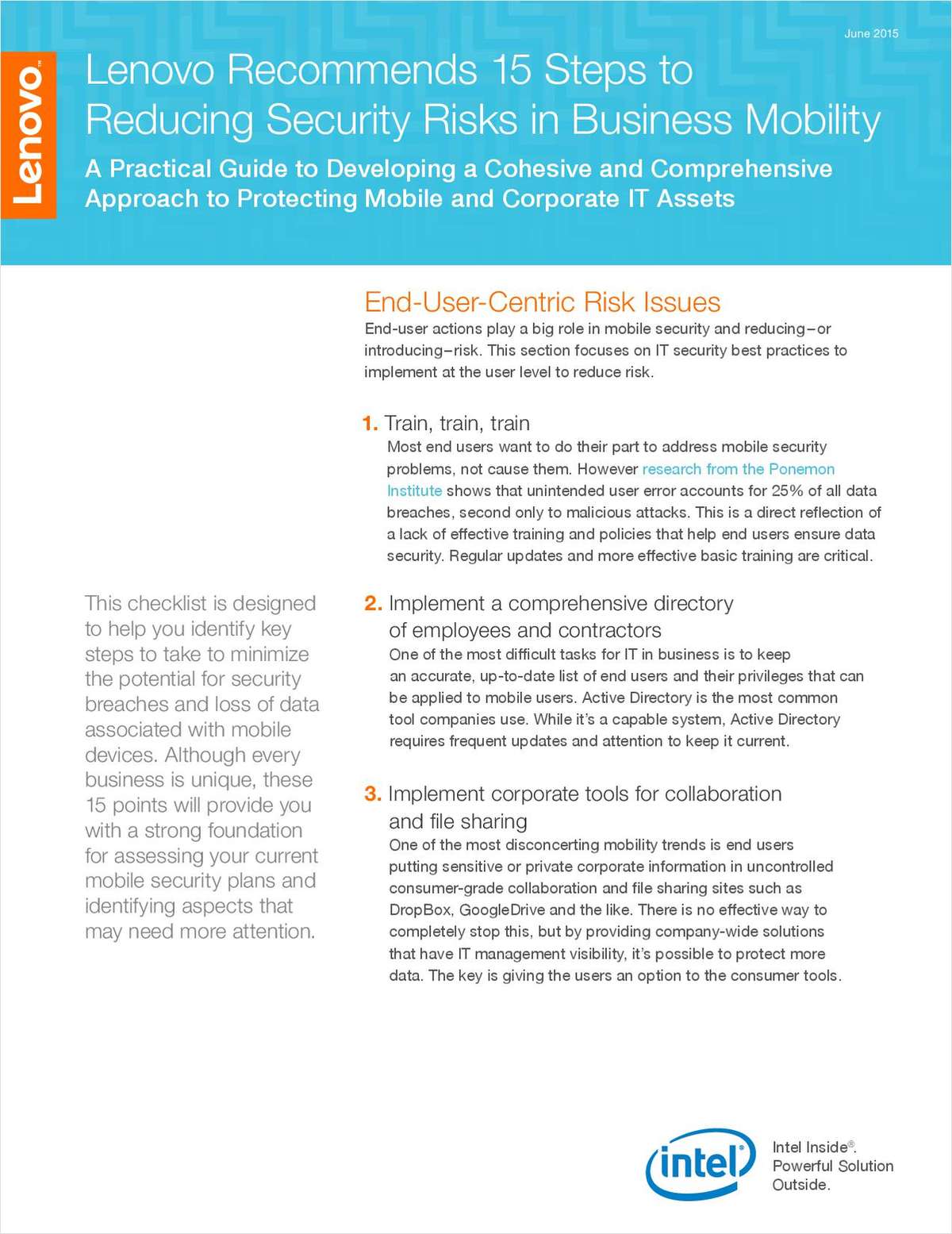
Whether it's misplaced devices or hackers infiltrating your systems, the risk of data loss and theft posed by mobile computing has never been higher. The good news: Companies can protect their most valuable data by creating a security strategy that combines end-user training with intelligent policies and device selection.
This checklist gives SMB owners a handy guide for how to minimize risks and maximize the benefits of your mobile approach. You'll learn why it's crucial to:
This checklist gives SMB owners a handy guide for how to minimize risks and maximize the benefits of your mobile approach. You'll learn why it's crucial to:
- Implement corporate tools for collaboration and file sharing
- Enlist end users by helping protect their private data
- Choose vendors with broad product lines
- Select devices with two factor authentication